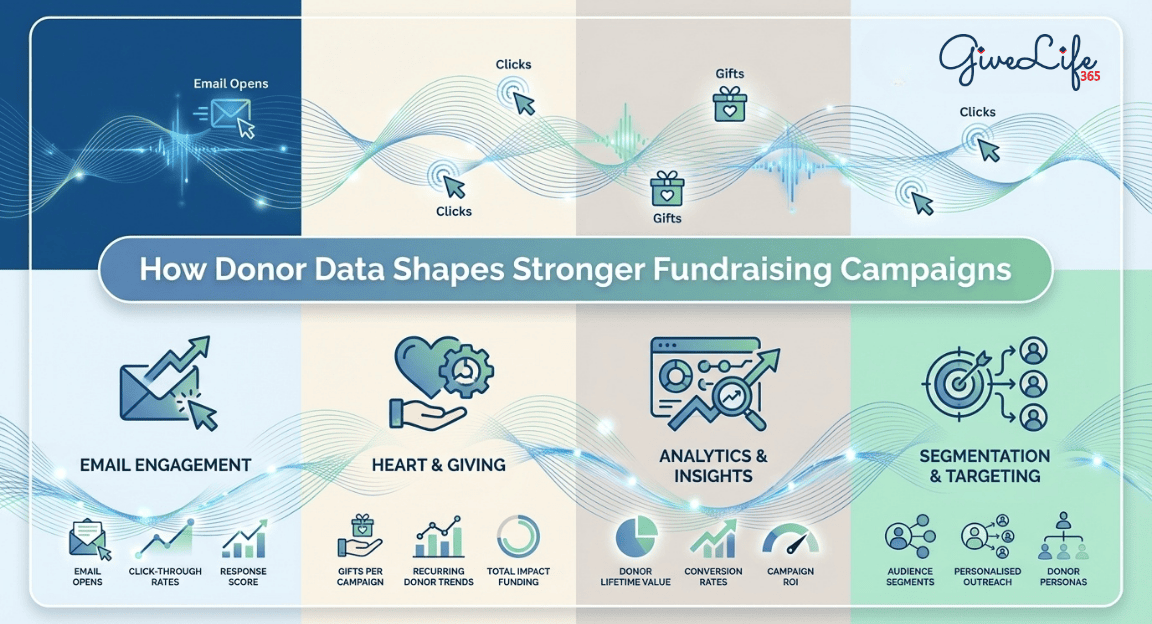
Use Donor Data to Improve Fundraising Campaigns
Learn how to use donor data for smarter fundraising. Segment donors, personalize asks, optimize amounts & boost campaign results with proven strategies.
Explore our latest articles for practical tips, success stories and insights tailored for nonprofit professionals. Whether you're streamlining operations, strengthening donor relationships, or finding smarter ways to work, our blog is here to support your mission—every step of the way.

